I recently got myself one of all the cheap chinese made handheld radios and wanted to share some things.
The model I got is a KSUN UV60-D
It covers a wide range of frequencies in RX/TX and an even wider range in RX.
It is also sometimes known as: Ksun TFSI X-TFSI Quans...
Link to the CTF itself
TryHackMe - Forensics
Type
Memory forensics
Challenge
Task 1 Volatility forensics
This is a memory dump of the infected system. Download the file attached to this Task.
The MD5 hash of the uncompressed file is: ba44c4b977d28132faeb5fb8b06debce
Download the vic...
Do you want to parse CDP or LLDP information? Do you run Windows 11? As I recently found out it might not be as straight forward as expected.
Turns out Microsoft removed some useful capabilities from the built in network tools from Windows 11.
After extensive searching and trying several tools,...
I was pondering how detection of AI generated text might work. Since GPT and the like are large language models (LLM) with varying context awareness they are basically Markov chains on steroids. Ofcourse none of the detect-AI-generated-text slingers really want to disclose their secret sauce as it w...
(aka OSINT for newbies, OSINT 101 or whatever else might get you interrested)
This article is meant as an introduction to OSINT for someone who is new to it. If you have previous experience it might come off as overly simple or lacking details, but hopefully there is still one or two things here f...
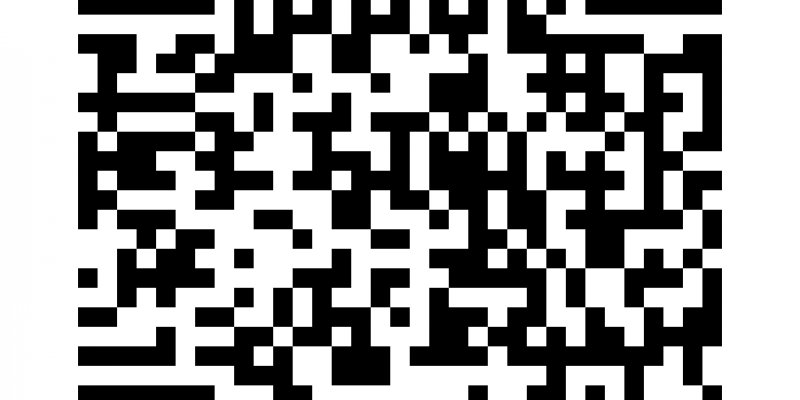
Android and iOS have since some time supported sharing wifi credentials via a qr code that other users can then scan with their camera app and join the network hassle free.
You might have also seen them printed at hotels, bars and various venues and thought you want that too.
That is very handy...